When you purchase through links on our site, we may earn an affiliate commission. This doesn’t affect our editorial independence.
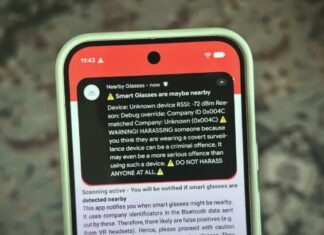
Google has responded to the complaint against it by releasing a Google Chrome security patch to address the vulnerability exploited by hackers in phishing attacks, urging users to update their browsers for better security.
Google said it has fixed a Windows Chrome browser vulnerability that malicious hackers have used to break into victims’ computers.
Google said in a brief note on Tuesday that it fixed the vulnerability, tracked as CVE-2025-2783, that was discovered by researchers at security firm Kaspersky sometime in March.
The company confirmed that it was aware of reports that an exploit for the bug “exists in the wild.” The bug is called a zero-day because the vendor, in this case, Google, was given no time to fix it before it was exploited.
According to Kaspersky, the bug was exploited as part of a hacking campaign targeting Windows computers running Chrome.
In a blog post, Kaspersky called the campaign “Operation ForumTroll” and said victims were targeted with a phishing email inviting them to a Russian global political summit. When a link in the email was clicked, victims were taken to a malicious website that immediately exploited the bug to access the victim’s PC data. It is believed that this attack necessitated the coming of the updated Google Chrome security patch.
Kaspersky provided specific information about the bug at the time of the Google Chrome security patch, but said that the bug allowed the attackers to bypass Chrome’s sandbox protections, which limit the browser’s access to other data on the user’s computer. Kaspersky said the bug affects all other browsers based on Google’s Chromium engine.
In a separate analysis, Kaspersky said the bug was likely used in an espionage campaign, typically designed to stealthily monitor and steal data from a target’s device, usually over some time. The Russia-headquartered security firm said the hackers sent personalized phishing emails to Russian media representatives and employees at educational institutions.
It’s unclear who exploited the bug, but Kaspersky attributed the campaign to a likely state-sponsored or government-backed group of hackers. However, the company has swiftly reacted by updating the Google Chrome security patch to protect its users.
Browsers like Chrome are a frequent target for malicious hackers and government-backed groups. Zero-day bugs that break through their protections and into the victim’s sensitive device data can be sold at high prices. Recall that in 2024, one zero-day broker offered about $3 million for exploitable bugs that can be triggered over the internet.
The company said the Google Chrome security patch will feature updates over the coming days and weeks.
You can also read the following: