When you purchase through links on our site, we may earn an affiliate commission. This doesn’t affect our editorial independence.
As of today, the internet has become a very important tool and resource, like a double-edged sword. It is easy and fast to get access to the information, download the things we want, connect with people, work, and do the homework. On the other hand, this technology might have put us at the gates of the new problems, giving the chance to the burglars, who are always finding new ways to take advantage of the system as well.
Cyber criminals as well as hackers are in search of chances everywhere. They not only target top companies but also ordinary people, groups of employees, and sometimes even government buildings. Your safe idea might be a huge mistake. These are the top cybersecurity risks. You don’t know that will change the way you see the internet and your privacy. Therefore, it is essential to recognize new threats and secure your privacy by learning how to reduce the risks of cybersecurity attacks.
1. Ransomware: Pay Up or Lose Everything
Just picture the feeling of helplessness after you discover that all your files—photos, documents, and personal data—have been kidnapped. A screen message appears and asks for a ransom in cryptocurrency; otherwise, everything will be completely gone.
This is nothing else but the ransomware, and it is considered to be one of the most dangerous cybersecurity threats.
Cybercriminals will encrypt your files and then ask for payment to get them back. If you don’t follow through on payments, you will lose everything. The ransomware attacks are also on the increase and are quite advanced using the fact that they now target corporate bodies, hospitals, and even government institutions. A few ransomware groups are involved in “double extortion”—apart from encrypting, they also threaten to release it if the ransom isn’t paid.
2. Phishing Attacks: The Ultimate Deception
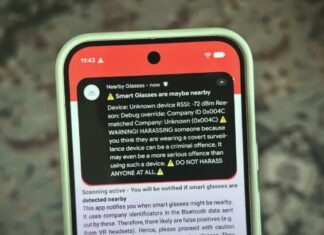
Now a days, the deception game is can be considered as one of the priminitve and refined plan of a cybercriminal. Phishing is the procedure of obtaining sensitive data by deceiving users into disclosing their credentials such as passwords, banking information and credit card numbers, etc. To do this, they send fraudulent emails, text messages, or even social media messages that fooled you into thinking that they were from authoritative sources.
The light of phishing is no longer just the emails of yesterday. Unfortunately, there are other forms of it – voice phishing, SMS phishing, and scam social media sites that they use to trap victims. They are difficult to detect because cybercriminals impersonate trusted people like banks, agents, delivery services, and even the place you work, and provoke the user to initiate the engagement by triggering fear, urgency, or curiosity.
How to Spot a Phishing Attack:
- Be careful about weird spellings or addresses that are not normal in an email.
- Do not open any links or attachments if they come out of the blue.
- Verify that messages the organization sends you contact them directly.
- In all your important accounts, set up two-factor authentication (2FA).
- Employ email security filters to receive alerts like phishing.
3. Deepfake Scams: When AI Becomes the Enemy
Deepfake technology can be disturbing in its existence and exceedingly extremely awe-inspiring. The application of AI-manufactured voice and video trading of real persons is operational for criminals on the side of the law. Think about a situation in which you would be called by your superior, inquiring for resources which are to be transferred, but nevertheless to an AI copy of your superior.
Scams done with deepfake technology are being done more on the corporate business fraud, political manipulation, and online blackmail. Criminals apply AI to imitate executives, stars, and even family members; through this, they produce videos or voice recordings that appear real. These scams have already been responsible for losses reaching millions of euros.
How to Protect Yourself:
- Getting an authentication of digital video or voice messages from another communication channel
- Raising awareness regarding deepfake media
- Questioning such urgent financial requests
- Taking up AI utilities that have the function of detecting anomalies in the suspicious media
4. Internet of Things (IoT) Attacks: Your Smart Devices Are Spying on You
Having Smart TVs, thermostats, and baby monitors connected to the internet is not uncommon in our homes. But you won’t be random if you think about it. That these devices often do not have security measures that are very strong thus they are the first choice for hackers.
IoT attacks that are carried out by hackers accomplish by taking over smart devices, looking through your activities, or supporting an attack by using them as part of a botnet. In some cases, hackers were successful in even reaching baby monitors to listen to families.
How to Stay Safe:
- Change default passwords on all smart devices.
- Review the latest firmware and install it.
- Use of a Wi-Fi network that is secure and has a strong password.
- Remote access to IoT devices should be disabled if it is not needed.
- Device activity should be monitored for things that are not normal.
5. Social Engineering: Hacking the Human Mind
The social engineering approach has no need for the utilization of brands. They just need to target people to get the stuff. Basically, it is the art of convincing someone to perform a task that will meddle with the security of sensitive data. This could happen whether it be a phone call, email, or a physical meeting.
Social engineering attacks target human psychology instead of technical issues. Attackers might act as contractors for IT, some government representatives, or even deceived loved ones. They engage victims in time-pressing situations in order to force them into the disclosure of the passwords, the transfer of the funds or the allowing of access to sensitive systems.
How to Avoid Falling Victim:
- Ask for sensitive information only upon verification of the request.
- Be suspicious of people asking for passwords and financial details.
- Personal information shouldn’t be shared on social media platforms.
- Prioritize training security awareness as part of the company workplace.
6. Malware: The Silent Killer
Malware is a general term for all kinds of software that is harmful, disruptive, or intent on stealing information. Included are items such as viruses, worms, Trojans, or spyware. Once you expose your device to malware, it will be able to keep an eye on your activities, take your private information, or even wipe data.
Advanced malware is often the spyware that security programs usually fail to detect; it hides within the legitimate applications as part of the process. Some forms of malware, such as keyloggers, can log everything that you type, including passwords and financial data.
How to Protect Yourself:
- Always have the most recent updates for your operating system and software.
- Utilize and regularly update antivirus software.
- Refrain from downloading files from unknown sources.
- Implement and use a firewall to filter incoming and outgoing traffic.
- Shun pirated software because it usually has malware.
7. Data Breaches: Your Information Is Already on the Dark Web
Every year, malware attacks result in the theft of sensitive information of millions of individuals. If you have ever used an online service, there is a good possibility that your information has already been leaked and is being sold on the dark web.
Cybercriminals frequently target businesses to acquire vast databases of user credentials, which are then sold or exploited for identity theft, fraud, and blackmail. Major corporations such as Facebook, LinkedIn, and Marriott have also been unfortunate enough to suffer security breaches affecting millions of users.
How to Minimize the Risk:
- Differentiate each of your online accounts with unique passwords.
- Use 2FA wherever possible.
- Find out if your email has been hacked.
- Be alert to the bank statements you receive and credit reports regularly.
8. Zero-Day Exploits: The Unknown Threat
A zero-day exploit is a cyberattack targeting a vulnerability in software that is unknown to developers. These vulnerabilities are called “zero-day” because there’s zero time to fix them before hackers exploit them. Cybercriminals use these flaws to gain access to sensitive data, plant malware, or take control of systems. Governments, cybercriminals, and even corporations sometimes use zero-day exploits for cyber espionage.
How to Protect Yourself:
- Make it a point to patch up vulnerabilities immediately. You can set your software to update itself automatically.
- Use a security system that will recognize potentially dangerous behavior.
- Subscribe to cyber defenses watchers and research studies to forecast risks and threats of new cyber processing.
9. Insider Threats: The Danger Within
The external world is not the only source of cyber threats. Insider threats arise when staff, contractors, or corporate partners exploit their access to programs and data illegally, threaten the organization’s safety, or lead to its downfall. The activity can be realized either purposely (espionage, revenge, fraud) or accidentally (phishing scams, weak security measures).
How to Prevent Insider Threats:
- Limit access to sensitive information to only those who need it.
- Conduct regular cybersecurity training to educate employees.
- Monitor user activity for suspicious behavior or unauthorized access.
- Implement strict access controls and multi-factor authentication.
10. Cryptojacking: The Secret Hijacking of Your Resources
Cryptojacking is a cyberattack wherein hackers stealthily employ your computer’s processing power for the purpose of cryptocurrency mining. Differentiating it from the ransomware, the crypto-jacking takes place without the user of the computer’s knowledge, and so it is that the usage of the computer slows down, there is an increase in its temperature, and the electricity bill rises.
How to Protect Yourself:
- Install browser extensions that block cryptojacking scripts (such as MinerBlock).
- Regularly monitor your CPU usage to detect unusual spikes.
- Use the antivirus and anti-malware software with complete scopes to detect the cryptojacking malware.
- Update your software and browser regularly to ensure that security breaches can be remedied.
Cybercriminals stretch both their skills to the limit as well as technology in order to commit crime and damage. Only by remaining informed and employing rigorous security practices can you get ahead of the curve.
Remain alert!